Oil and Gas: A Comprehensive Analysis of Offensives Against Perimeter Devices
4.7 (625) In stock

Since 2010, malware such as Stuxnet, Flame, and Mini-Flame, along with Shamoon and Triton, have disrupted operations, with Saudi Aramco's 2012 Shamoon attack as a prime example.
First Amendment Handbook RCFP Newsgathering Guide

Research & development in oil & gas industry

Sustainability, Free Full-Text
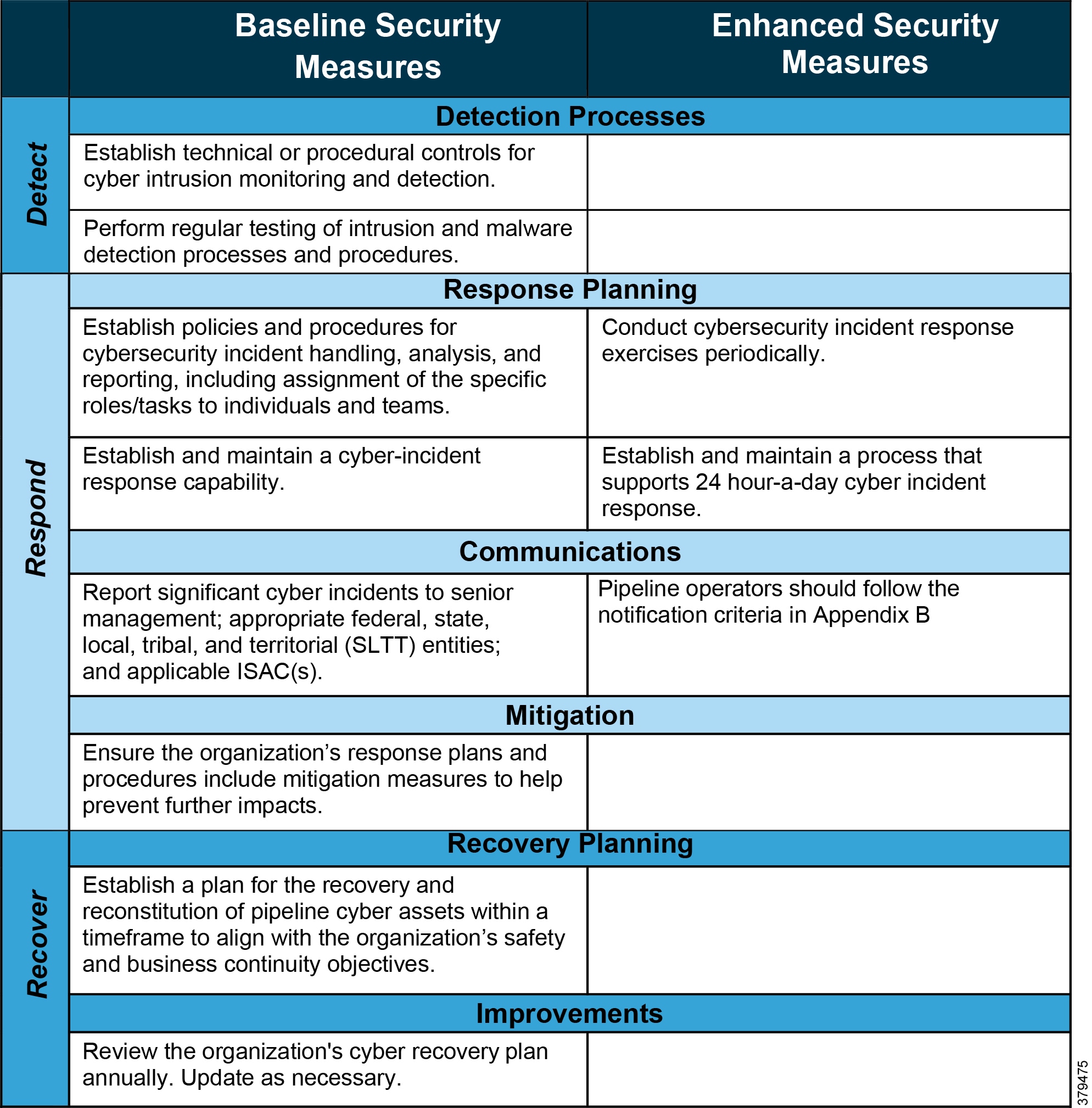
Oil and Gas Pipeline Security Reference Document - Oil and Gas

Chemical and Sensory Characteristics of Soy Sauce: A Review

White Papers TXOne Networks

How the Federal Government Can Hold the Oil and Gas Industry

Relationship between GDP Growth, Energy Consumption and CO2

TXOne Networks - CYBERSEC 2024

WESTCON Redes e Conectividade Industrial no LinkedIn: #iadbrasil #schneiderelectric #automacaoindustrial #automaçãoindustrial #ra

Nyhetsbrev OT-Säkerhet #57

In the news - Africa's premier report on the oil, gas and energy

Kelvin Kamimura no LinkedIn: #altivar #atv650 #atv950

Think Tank reports on the invasion of Ukraine - Consilium

WESTCON Redes e Conectividade Industrial no LinkedIn: Encontro Técnico Virtual – Tecnologias Habilitadoras para IIoT
Perimeter Security - Brassets Group
Perimeter Medical Imaging - Tech Stack, Apps, Patents & Trademarks
Symantec acquires Luminate Security, makers of software-defined perimeter technology
DFG Perimeter Technologies®️ Receiver Battery - Dog Fence Guy
10000001 Underground pet containment system User Manual Perimeter




:format(webp)/https://static-sg.zacdn.com/p/hm-5688-2354123-1.jpg)
