Dark endpoints: an invisible threat to your IT team
4.6 (353) In stock

Invisible devices create significant blind spots that can leave IT departments helpless to act against a breach until it is already too late. A new report from Absolute found 13% of enterprise devices aren't connected to the corporate domain.
The Absolute platform delivers self-healing endpoint security and always-connected IT asset management to protect devices, data, applications and users — on and off the network.

Blog, Cybersecurity Trends and Tips

Deconstructed Podcast: How the U.S. Makes Its Wars Invisible
Understanding Privilege Escalation and 5 Common Attack Techniques

Endpoint Security Is Not Enough to Thwart Advanced Threats

Carbon Black Next-Gen Antivirus Checklist

Cybersafe Spotlight: SOL Dark Web
Are You Familiar with the Monster in the Cloud?
Everything You Need to Know About AI Cybersecurity

How to Make Cybersecurity Effective and Invisible

security Blog Category

6 Charts That Show What Is and Isn't Working in Endpoint Security
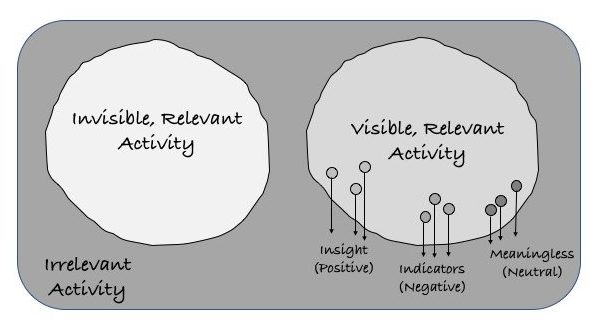
What Does Cyber Visibility Mean to You?
What is the dark web?

Insider threats and their affect on endpoint security
Womens Absolute Invisible Smooth Contour Bra Black, Pink
Chantelle Absolute Invisible Smooth Push-Up Bra Black
Chantelle Absolute Invisible Smooth Push-up Bra In Beige | ModeSens
Chantelle Nude Absolute Invisible Smooth Underwire Strapless Bra L11305 Size 38B
 Job openings reach record highs in 2022 as the labor market
Job openings reach record highs in 2022 as the labor market 500G Women's Extra Thick Leggings Tights Bare Leg Artifact Women's Nude Skin Color Warm Thick Tights Fall/winter One-piece Pants With Velvet Leggings
500G Women's Extra Thick Leggings Tights Bare Leg Artifact Women's Nude Skin Color Warm Thick Tights Fall/winter One-piece Pants With Velvet Leggings Aura Flared Pant - Glacial Lake
Aura Flared Pant - Glacial Lake SARAH PACINI PURPLE MADE IN ITALY 100% COTTON ASYMETRICAL BUTTON UP BLOUSE
SARAH PACINI PURPLE MADE IN ITALY 100% COTTON ASYMETRICAL BUTTON UP BLOUSE Jockey Denim Melange Capri Pants for Women #1300 [New Fit
Jockey Denim Melange Capri Pants for Women #1300 [New Fit Prana Verde Yoga Mat
Prana Verde Yoga Mat